I just found an undocumented feature in ProtonMail… which I thought you might find useful to know.
Backstory
I use ProtonMail as my primary email hosting provider nowadays, as it gives me convenient PGP encryption across my devices, and all incoming emails that are not already PGP encrypted will be encrypted with my public key, meaning emails are encrypted at rest.
I never had an issue with spam, until yesterday… Yesterday, I suddenly started receiving spam, and they’re all the same kind: “Invest X amount and get Y in return”, but from a different sender (address) in each email, but I do believe it might be the same person (or people) behind this.
All these spam emails target the same email address of mine… or so I thought. At first, I was worried there might have been a breach somewhere and my email address leaked, but I think I have a different explanation:
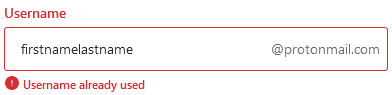
Without revealing too much, the email address they targeted is a very generic one, of the first name and last name kind, no dots, hyphens or underscores in between…
…but the spam emails I’m getting target firstname.lastname, firstname-lastname and firstname_lastname… all with a dot, hyphen or underscore.
So, clearly it could not have been a breach since I don’t use that ProtonMail address with dots, hyphens or underscores anywhere.
That’s when it hit me: Someone must have started brute forcing ProtonMail addresses, using a list of possible names (and patterns) just hoping the email address exists, and clearly it works.
The reason I believe it must be the same person (or people) sending these, is because the spam all started coming in the same day, it’s all the same type (different content but same type) and they all seem to be guessing email addresses.
The ProtonMail feature
So, as it turns out, ProtonMail “ignores” the hyphens, dots and underscores. While sadly, I did not find anything about that in the official documentation, I did find ProtonMail confirming this in several places of their Subreddit (by /u/ProtonMail, which is the official ProtonMail account). I also did test it by sending myself emails with lots of random dots, hyphens and underscores, which all arrived.
Why is this feature useful? Well, other than to receive spam, it’s actually useful when someone isn’t sure whether there was a dot, hyphen or underscore between your names and sends it to the “wrong” address, and you will still receive it.
But that’s not the intended use-case, actually: According to /u/ProtonMail it’s so that when you’re talking to someone, say a journalist, with the email address journalistname at protonmail dot com, an attacker can’t just create an account as journalist.name at protonmail dot com and email you, which might be just a small enough detail that you don’t notice and respond thinking it’s someone else than it actually is.
The Gmail feature
If you’ve used Gmail, you might know that Gmail has this same feature, but limited to just the dot.
The Email semi-alias feature
On another note, you might know that the + (“plus sign”) separator is a standard email feature (not necessarily supported by all providers), where you can create virtually unlimited email addresses by adding a plus sign at the end before the @ (“at”) symbol, followed by anything you like. For example, firstnamelastname+something at domain dot com.
Both Gmail and ProtonMail do support this. It’s handy if you want to sign up to a website, where you can give them email+website at example dot com, and if you ever start receiving spam on that address you will know that “website” leaked it, and you can block all emails going to that address.
Author’s notes
Please note that my email address is not exactly first name and last name, but a similarly common pattern, so if you happen to know me in person, please don’t try emailing to some guessed address. I’d also like to apologize for the weird formatting of email addresses (spelled out) and would like to explain that this is because crawlers on the web would otherwise pick up on them and start spamming there. I’m sure someone thought it would be funny to create an email address with literally “firstnamelastname”, and I wouldn’t want them to start receiving spam…
Update August 7th – 06:55
I can now confirm with high certainty that it’s the same person/people behind these spam emails that I’ve been receiving because I took a closer look at the links in those emails, and they all point to the same location, with an ID as a parameter that is also always the same.
Hey, thanks for your research!
I have the same problem and couldn’t find official information on it.
It’s good to know that other people have the same issues :)
Haaa finally a precise answer to my questions !
So I am also on Protonmail, and I have exactly the same problem, and it appeared about the same time as you. It started around Thursday 05 August 2021.
A new spam every day. The attacker is trying, one day he wrote my address (for example) “word at protonmail”, the next day “wor.d at protonmail”, etc., but they all come to me.
Indeed, I didn’t find any information about the fact that Protonmail ignores the points in their documentations. Thanks for the info ;)
On the other hand, the links that appear in his emails do not point to the same places. Looking through Whois, there was one in Chile, the other in the USA etc.
But I know it’s the same person, since it’s the same kind of message every time. A really basic message without any effort.
If you scan the addresses on VirusTotal, they are flagged as spam or malware.
The attacker’s addresses, seem normal, it’s info at …, or mail at … . These could be hacked and used websites.
This is an address I have had since 2017, without ever having received a attack. This week I had finally started using it, and after just two days of use, this attack started. It was driving me crazy… I thought I was going to get a clean start and get over my past mistakes, and now it’s still happening ?!
I’m glad to see that it’s not at all due to a mistake on my part :)
Thank you for the comment! It’s nice to get some additional confirmation/insight into this. (: